Never Lose a Byte: A Deep Dive into TCP Working
How the Transmission Control Protocol turns an unreliable network into a perfect delivery system.
Have you ever wondered how the email arrives with every word intact, or how does the file remain intact on download without any missing piece of information? The answer lies in the protocol- TCP (Transmission Control Protocol). Unlike other methods that just transfers data onto the internet to transfer, TCP does reliable transfer of data, making sure the data is not corrupted or lost.
What is TCP?
TCP (Transmission Control Protocol) is a transport layer protocol which is is a connection-oriented and reliable. It's part of the TCP/IP protocol suite and operates at Layer 4 (Transport Layer) of the OSI model.
Key Characteristics of TCP:
Connection-Oriented: TCP establishes a connection between sender and receiver before data transfer begins.
Reliable: TCP guarantees accurate delivery of data. In case of a failure, the application will be notified.
Ordered: Data arrives in the same order it was sent, even if packets take different routes.
Error-Checked: TCP does a error check to know for corrupted data-packets or packet loss.
Flow-Controlled: TCP manages the rate of data transmission to match the receiver's processing speed.
Congestion-Controlled: TCP adjusts transmission rate based on network conditions.
Hence, TCP prevents packet loss, unordered data packets delivery, data corruption, duplicate packets, flow control, and congestion control.
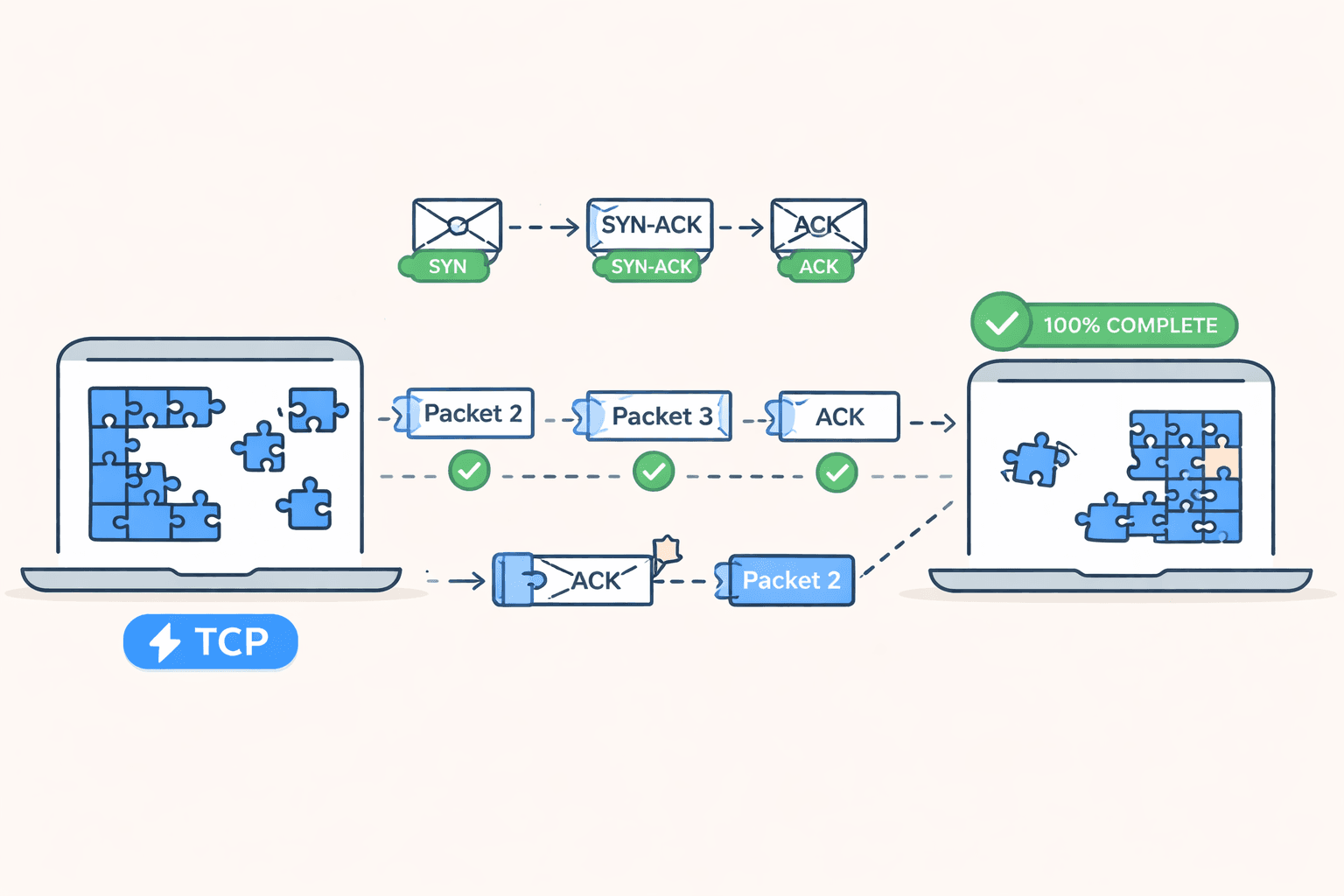
The TCP 3-Way Handshake: Establishing Connection
The TCP establishes a connection with the receiver through three-way handshake before the actual transfer of data occurs. This connection is same as two people talking over phone, getting acknowledgement of the other person presence before starting the conversation.

Step 1: SYN (Synchronize): Client → Server
The client in order to connect to server, sends a SYN packet with:
SYN flag set to 1: Denoting the request is a synchronization request. After sending SYN, the client enters the
SYN-SENTstate and awaits server's response.Initial Sequence Number (ISN): A random number (eg 1000). A random number is used due to security reason. It prevents the attackers to predict the sequence and hijack the connection.
This is the client saying: "I want to talk to you, and I'll start counting my bytes from 1000."
Step 2: SYN-ACK (Synchronize-Acknowledge): Server → Client
If the server accepts the connection, it responds with:
SYN flag set to 1: The server is also synchronizing
ACK flag set to 1: Acknowledging the client's SYN
Server's ISN: Another random number (eg: 2000)
Acknowledgment number: Client's ISN + 1 (eg. 1001)
The server is saying: "I got your bytes starting at 1000. I'm ready, and I'll start counting my bytes from 2000. Send your next byte as 1001." The server enters the SYN-RECEIVED state.
Step 3: ACK (Acknowledge): Client → Server
The client completes the handshake with:
ACK flag set to 1: Acknowledging the server's SYN-ACK
Acknowledgment number: Server's ISN + 1 (eg: 2001)
The client confirms: "I got your byte starting at 2000. I'm ready to receive your next byte at 2001."
The connection is then ESTABLISHED after the final ACK. The client and server know they can communicate and the network path is working.
Sequence Numbers: Every byte of data gets a sequence number. If the client sends 100 bytes starting at sequence 1001, those bytes are numbered 1001-1100.
Acknowledgment Numbers: The receiver sends back an ACK with the next sequence number it expects.
Example Flow
Client sends: Sequence 1001, 100 bytes of data
Server receives: Bytes 1001-1100
Server ACKs: Acknowledgment 1101 (expecting byte 1101 next)
Client sends: Sequence 1101, 50 bytes of data
Server receives: Bytes 1101-1150
Server ACKs: Acknowledgment 1151

This continues until all data is transferred.
How TCP Ensures Reliability, Order, and Correctness
Ensuring Reliability: Retransmission
TCP uses acknowledgments and timers to guarantee delivery.When data is sent, TCP starts a retransmission timer
If an ACK isn't received before the timer expires, TCP retransmits the data
The timer duration is dynamically calculated based on network conditions (RTT - Round Trip Time)

Ensuring Order: Sequence Numbers
When packets arrive out of order, TCP buffers them until all previous data arrives.Receives packet 1 (1001-1100) → Delivers to application
Receives packet 3 (1201-1300) → Holds in buffer (waiting for 1101)
Receives packet 2 (1101-1200) → Delivers both packet 2 AND packet 3 in order

Ensuring Correctness
Every TCP segment includes a checksum calculated over:TCP header
Data payload
Pseudo-header (including IP addresses)
Flow Control: The Sliding Window
TCP prevents overwhelming the receiver using a receive window:The window size tells the sender: "I can buffer this many bytes right now."
As the receiver's buffer fills up, it reduces the window size. If the buffer is full, it sets window = 0, temporarily pausing transmission.
Congestion Control
TCP adjusts its sending rate to avoid network congestion using algorithms like:Slow Start: Start slow, gradually increase speedCongestion
Avoidance: Carefully increase when network is stable
Fast Retransmit: Quickly retransmit when loss is detected
Fast Recovery: Reduce sending rate when congestion occurs
Closing a TCP Connection: The 4-Way Handshake
TCP is full-duplex, meaning both sides can send data independently. The termination process ensures both sides finish sending their data before the connection is fully closed.

Step 1: Client sends FIN
Client informs the receiver it has no more data to send.
Client can still receive data
Step 2: Server sends ACK
Sercer acknowledges the client is done sending data
Server can still send remaining data
Step 3: Server sends FIN
- Server informs client it is done sending data
Step 4: Client sends ACK
Client acknowledges the server is done sending data
Connection fully closed
This is called a graceful shutdown because both sides agree to close and ensure all data is delivered.
The Complete TCP Connection Lifecycle

TCP is an example of remarkable engineering because it turns the unreliable best-effort network into a reliable communication channel. TCP accomplishes this through a variety of methods, including the 3-way handshake, sequence numbers, acknowledgements, checksums, flow control, and congestion control to ensure that you receive your data exactly as you sent it.
When you are surfing a website, sending an e-mail, downloading a file or streaming video, TCP is running behind the scenes doing everything it can to ensure that all of the networking aspects are taken care of. Understanding TCP will give you a better understanding of how the internet communication technology works at its core and how elegantly designed solutions can be applied within the confines of an unreliable medium.
The next time you click on a hyperlink or send a message think about how incredibly intricate the movement of packets, acknowledgements, and coordination are between you and the person who is receiving your message through TCP.